Find the Right
Security Stack
Compare VPN, antivirus, and password managers.
NeoGuard provides the guides to help you choose.
0
vulnerabilities disclosed in 2026
(and it's only May)
What you're up against
Modern threats don't come one at a time. They compound.
Where do I start?
The right security setup depends on where you are.
Latest Articles
Practical guides on privacy, security, and compliance for businesses and individuals in Switzerland.
-

Proton Pass: Can the new AI Access Tokens make AI agents safer?
Proton Pass now offers AI Access Tokens for AI agents. We explain what they can do, where their limits lie, and how SMEs can put them to use.
-
Verizon DBIR 2026: Three Numbers Every SME Should Know
The Verizon Data Breach Investigations Report 2026 is out. Three numbers on third-party breaches, ransomware, and Shadow AI that matter to SMEs.
-
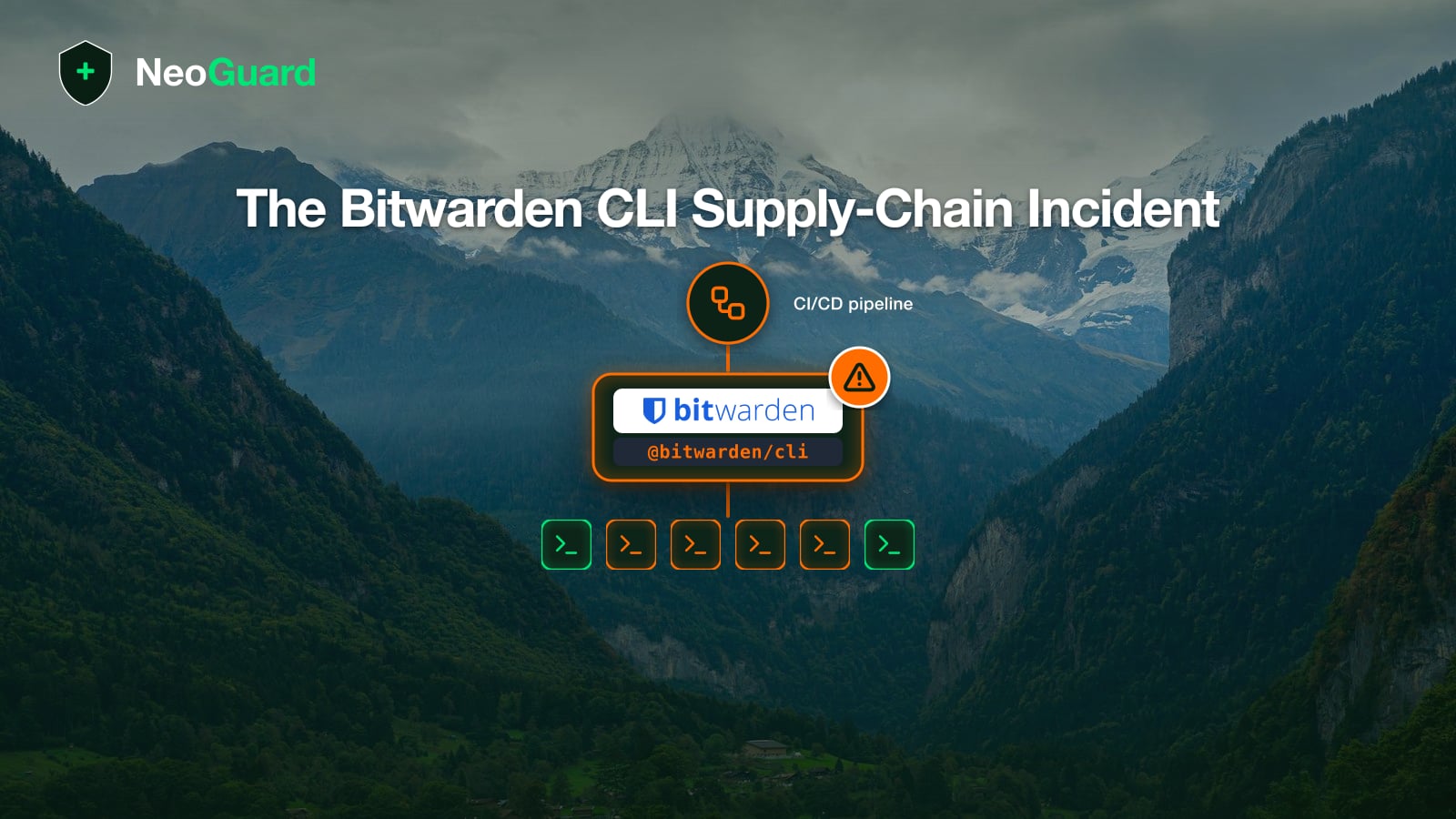
Bitwarden CLI Incident: Is Your Password Manager Still Safe?
On 22 April 2026 the npm package @bitwarden/cli was compromised. This article explains why vault data was not affected and when you should rotate secrets.
Privacy & Security Glossary
Key terms explained, from nFADP to endpoint protection.
- 2FA (Two-Factor Authentication)
- A security method that requires two different forms of verification before granting access, typically a password plus a code from a device you own.
- Backup
- A copy of your data stored separately from the original, allowing recovery after data loss from ransomware, hardware failure, accidental deletion, or natural disaster.
- BACS (Federal Office for Cybersecurity)
- Switzerland's federal cybersecurity authority (Bundesamt für Cybersicherheit), responsible for national cyber threat monitoring, incident coordination, and the mandatory 24-hour reporting requirement for critical infrastructure.
- Credential Stuffing
- An automated attack that uses stolen username/password pairs from one data breach to attempt logins on other services, exploiting the widespread habit of password reuse.
- Dark Web
- A part of the internet only accessible through specialized software (like Tor), where stolen credentials, personal data, and hacking tools are frequently traded on anonymous marketplaces.
- DDoS (Distributed Denial of Service)
- An attack that floods a website, server, or network with traffic from thousands of sources simultaneously, overwhelming it and making it unavailable to legitimate users.
Compare tools for your security stack.
Browse Guides