Credential Stuffing: One Reused Password, Many Compromised Accounts
TL;DR
- Password reuse is still widespread. Only around 6 percent of leaked passwords are unique.
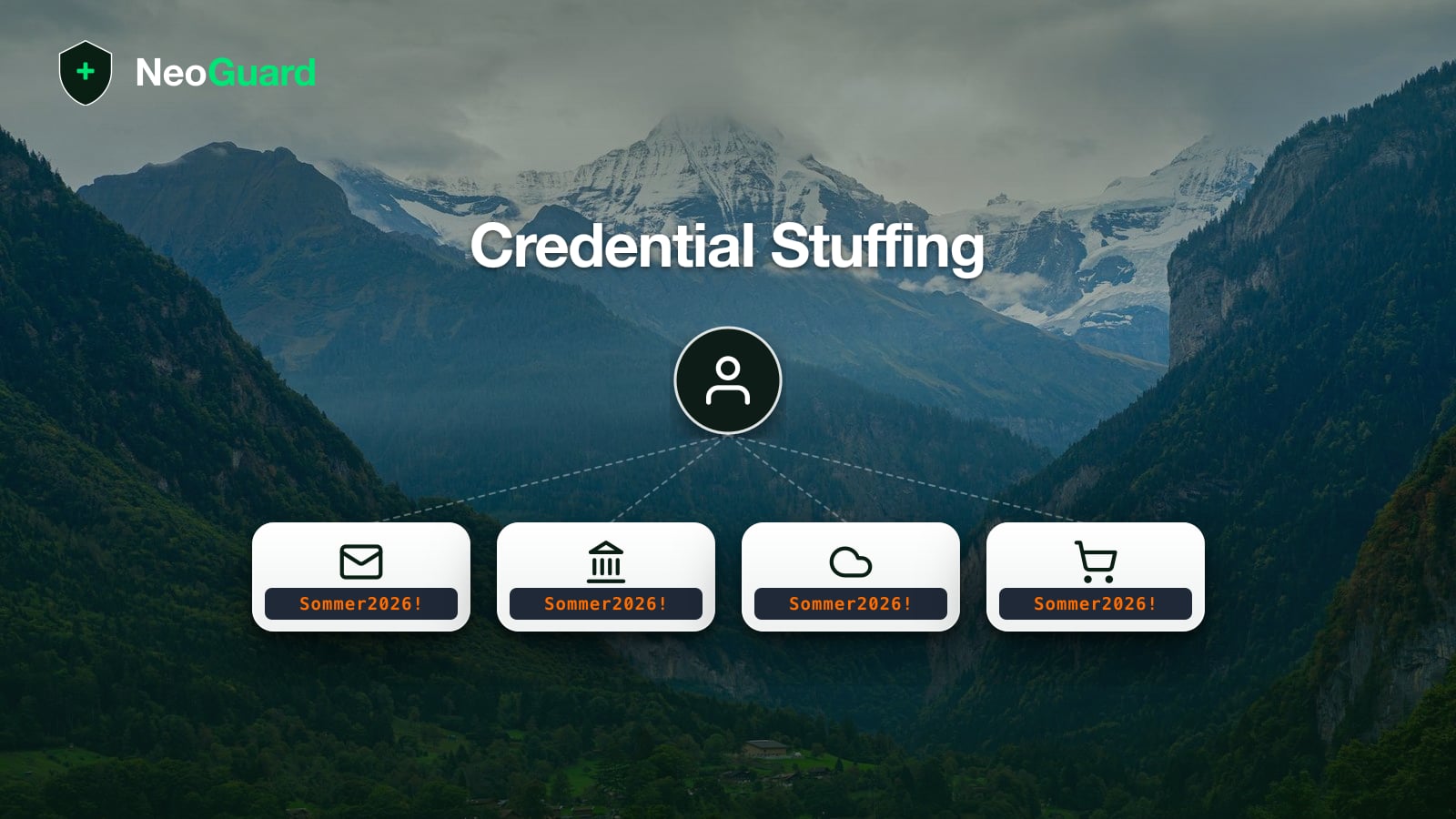
- Attackers don’t need to know which other services you reuse the same password on. They test leaked credentials automatically against many popular online services (credential stuffing).
- Patterns like
Summer2025!andSummer2026!only make passwords more predictable to attackers. - One of the most effective single measures is still a password manager that generates a unique, random password per service, complemented by passkeys where available and 2FA on important accounts.
When your email address shows up in a data breach, your first reaction is usually a small jolt of panic. Then the reassurance kicks in. I barely use that service anymore, no one else knows the password. The assumption sounds logical, but it’s exactly the gap credential stuffing has been exploiting for years. In an analysis of leaked passwords, Cybernews concluded that only a small fraction are unique. This reuse is the foundation of the entire attack type.
What is credential stuffing?
Credential stuffing is an automated attack where an attacker takes a list of email addresses and passwords from earlier data breaches and tries those combinations against many other services. For the Data Breach Investigations Report 2025, Verizon analyzed single sign-on (SSO) logs and found that the median enterprise platform sees 19 percent of daily authentication attempts coming from credential-stuffing tools, with larger organizations reaching 25 percent. Switzerland’s Federal Office for Cyber Security (BACS) also warns in its current S-U-P-E-R campaign that attackers automatically test stolen credentials on other platforms. The email account is especially critical, because it lets attackers reset passwords for other services.
Here’s where the misconception shows. Many people assume a leaked password is known to no one else, and no one would know which other services it’s still in use on. That’s literally true, but it’s beside the point. The attacker doesn’t need to know. They take the email address and the leaked password and test the combination automatically against Gmail, Outlook, Microsoft 365, iCloud, AWS, GitHub, PayPal, Twint, Amazon, Steam, Netflix, and so on. Each attempt takes a fraction of a second, and an attacker can run tens of thousands of accounts in parallel. The success rate per list is only a few percent, but with large datasets in circulation, even a few percent adds up to many compromised accounts.
How this chain plays out in practice was documented by BACS back in 2024. In a Swiss case with over CHF 20,000 in damages, the victim entered a password from a seemingly unimportant website on a phishing page. The attackers then used that one password to log in to other accounts in sequence, eventually emptying a crypto wallet. The entry point was a single password, reused in one place.
How does credential stuffing differ from password spray?
Credential stuffing is often equated with “brute-force attacks.” That is imprecise. It’s worth separating three related attack types, because the defense looks slightly different for each.
- Credential stuffing. The attacker has real email/password pairs from a data breach and tries them against many services, looking for accounts where you reused the same password.
- Password spray. The attacker has a list of email addresses but no matching passwords. Instead, they try a few very common passwords (
Welcome1,Summer2026!, orCompany2025!) against every email address, looking for accounts with weak or predictable passwords. - Brute force. The attacker systematically tries every possible character combination or dictionary word against a single account. Login limits and lockouts on the provider side make brute force less common in practice than the other two.
Credential stuffing exploits reuse, password spray exploits predictability. A password manager that generates a unique, random password per service neutralizes both attack types at once.
The Midnight Blizzard incident in early 2024 shows how effective password spray can be even against well-secured organizations. The state-sponsored actor used a password spray against a legacy test account without MFA to gain access to Microsoft corporate accounts, including emails of senior leadership. The method was low-and-slow, meaning few attempts per account and only very common passwords, keeping it under typical lockout thresholds.
Do patterns like Summer2026! help?
Just as common as “no one else knows this password” is the assumption that a pattern with minor variation buys security. Summer2025! for Gmail, Summer2026! for Office 365, Winter2025! for the bank. What feels like a reasonable compromise to someone who has to memorize passwords is a familiar pattern to an attacker.
Common cracking tools have been applying rule-based mutations to known wordlists for years. Append the year, capitalize the first letter, add a special character at the end, or replace a with @. If Summer2024! shows up in a data breach, Summer2025! and Summer2026! are automatically included in the next attempts. These predictable patterns are also the prime target for password-spray attacks. The attacker doesn’t need your leaked list at all, they just guess Summer2026! against a thousand email addresses and get hits.
What does AI change about the threat?
Pattern-based password cracking isn’t new. Hashcat mutation rules have been in widespread use for years. What generative AI changes is the cost of the personalized variant.
Reconnaissance against individual people used to be expensive. Anyone wanting to derive your likely password pattern from your public profiles (a dog’s name, a favorite team, a child’s birth year, or a favorite album) had to research manually. The building blocks for an automated version are all in place today, from AI-driven profile scraping to handoff into mutation rules. Anthropic writes in its August 2025 Threat Intelligence Report that Claude Code was used in multiple cases for credential attacks and Active Directory reconnaissance. In November 2025, Anthropic documented the first AI-orchestrated cyber espionage campaign, in which Claude extracted credentials and built network maps largely autonomously.
A password with personal context is easier to guess today. Even if no one is specifically targeting you, the research is running in the background.
What can you do?
Four measures close most of the attack surface that credential stuffing and password spray exploit.
- Use a password manager. It generates a unique, random password for every service. A manager like NordPass, 1Password, or Proton Pass generates and autofills credentials, so reuse never becomes a temptation. Our Password managers for SMEs in Switzerland guide breaks down which manager fits which team.
- Use passkeys where services offer them. Passkeys replace the password and the second factor in one step, are bound to the domain, and can’t be intercepted by phishing proxies. Many password managers already store passkeys.
- Enable 2FA on the important accounts. Email, banking, cloud storage, and identity providers belong here. Microsoft pegs the effect of modern MFA in the Digital Defense Report 2025 at over 99 percent of unauthorized login attempts blocked, so a second factor largely prevents automated sign-ins with leaked passwords. SMS codes can be hijacked via SIM swap, so TOTP apps are the more solid default. For admin and owner accounts, hardware keys like YubiKey or Titan are recommended; like passkeys, they are bound to the domain and therefore also defeat real-time phishing proxies.
- Enable breach monitoring. Services like Have I Been Pwned or your password manager’s built-in monitoring (1Password Watchtower, NordPass Breach Scanner, or Pass Monitor in Proton Pass) alert you when one of your email addresses appears in a new data breach. That lets you rotate the affected passwords promptly.
Credential stuffing only pays off for attackers as long as passwords get reused. Once you set a unique password per service or use passkeys, their success rate goes to zero. That is why a password manager is the structural answer to one of the most common identity attacks.
NeoGuard may earn a commission if you purchase through our links. This does not affect our editorial recommendations. See our privacy policy for details.